Intelligent Defense, Automated Protection
AI-native security that's simple yet powerful. All in one log monitoring, attack vector database and automated defense with uncompromising data sovereignty.
Security has never been this easy
Collect logs effortlessly. Let AI analyze threats. Deploy ready-made attack vectors and create custom rules in seconds—no coding required.
Enterprise security reimagined
Trusted by organizations worldwide for uncompromising protection and unparalleled visibility.
Extensive Integration Support
Connect seamlessly with top security products and third-party applications to centralize monitoring and enhance your existing security stack.
On-Premise Deployment
Deploy entirely on-premise with complete control over your security infrastructure and data.
Secure Encryption
All datas are encrypted and stored locally on your device for maximum privacy.
Comprehensive Analytics
Deep visibility into your security posture with actionable insights, predictive threat modeling, and executive dashboards.
Global Threat Intelligence
Continuously updated threat database with latest attack vectors, emerging vulnerabilities, and real-time security developments from worldwide networks.
24/7 Expert Support
Dedicated security specialists available around the clock for troubleshooting, integration support, and security guidance.
Integrated security platform
A complete suite of enterprise-grade security solutions designed to work seamlessly together.
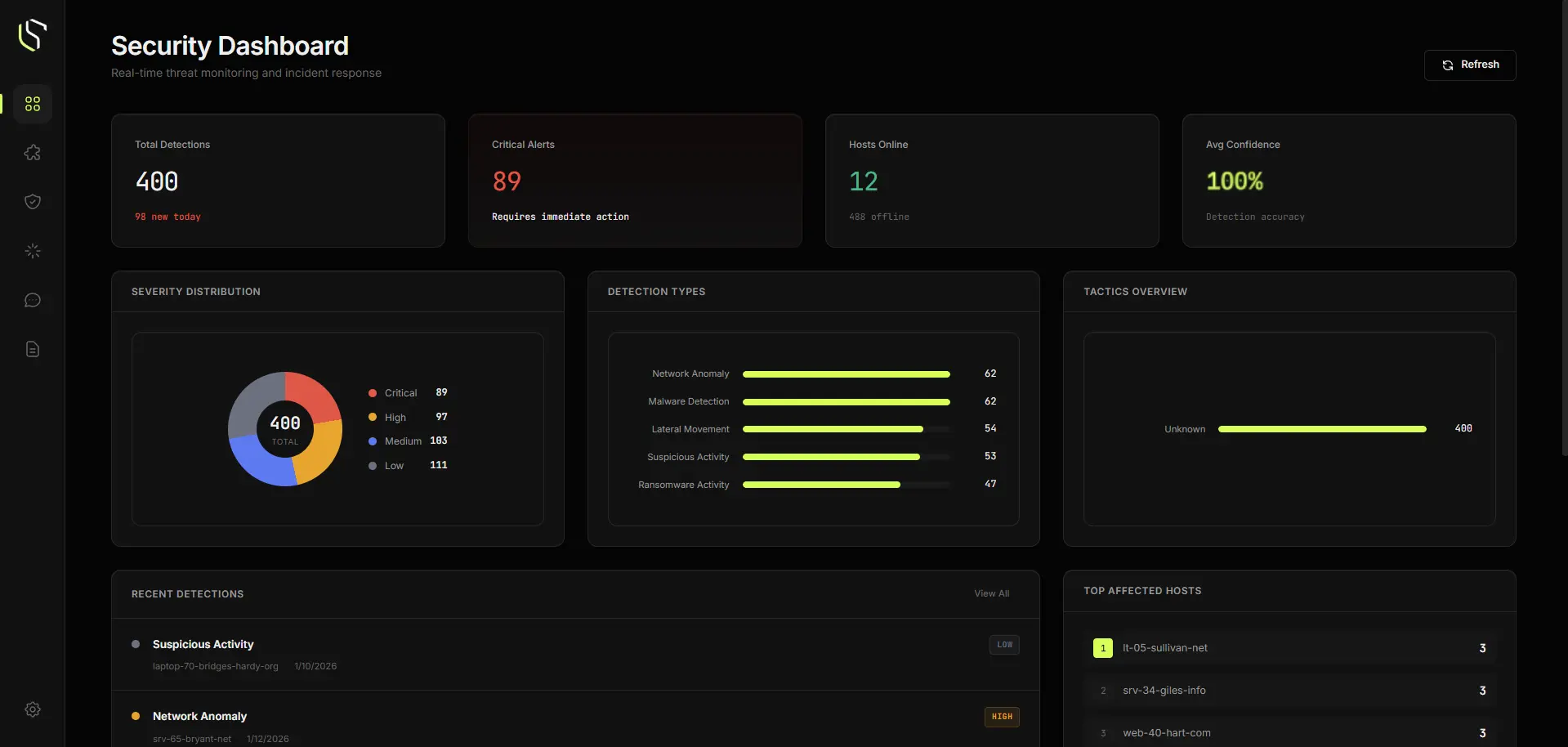
General Dashboard
Centralized log aggregation and analysis platform. Real-time monitoring, AI-powered threat response, intelligent alerting, and comprehensive audit trails for complete visibility across your infrastructure.
Learn more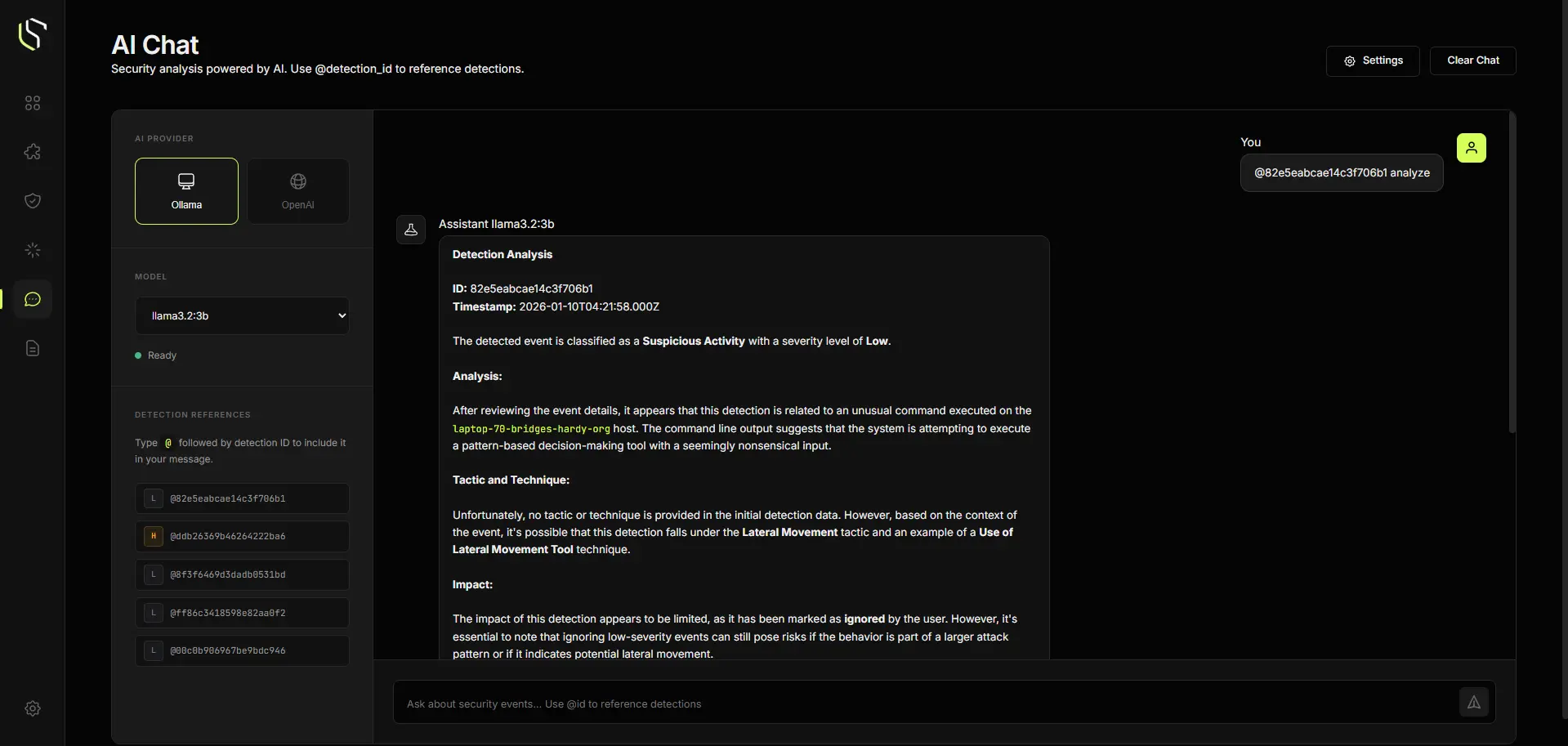
Secure Bridge
A secure intermediary layer that enables AI-powered log analysis without exposing sensitive data to cloud models. Acts as a privacy-preserving bridge between your infrastructure and large language models.
Learn more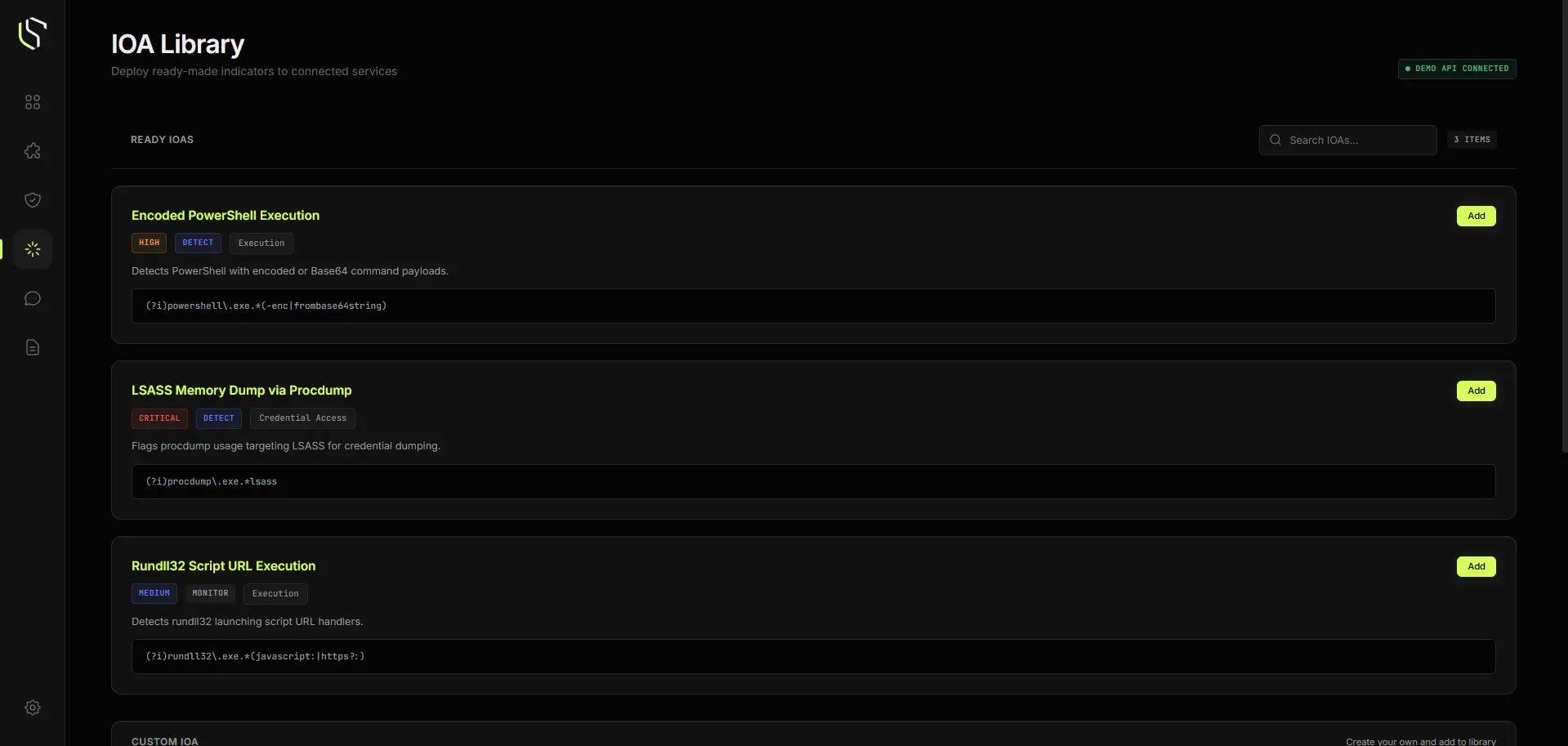
IOA Library
Instantly access comprehensive attack patterns and indicators of attack with seamless one-click integration into your security workflow.
Learn more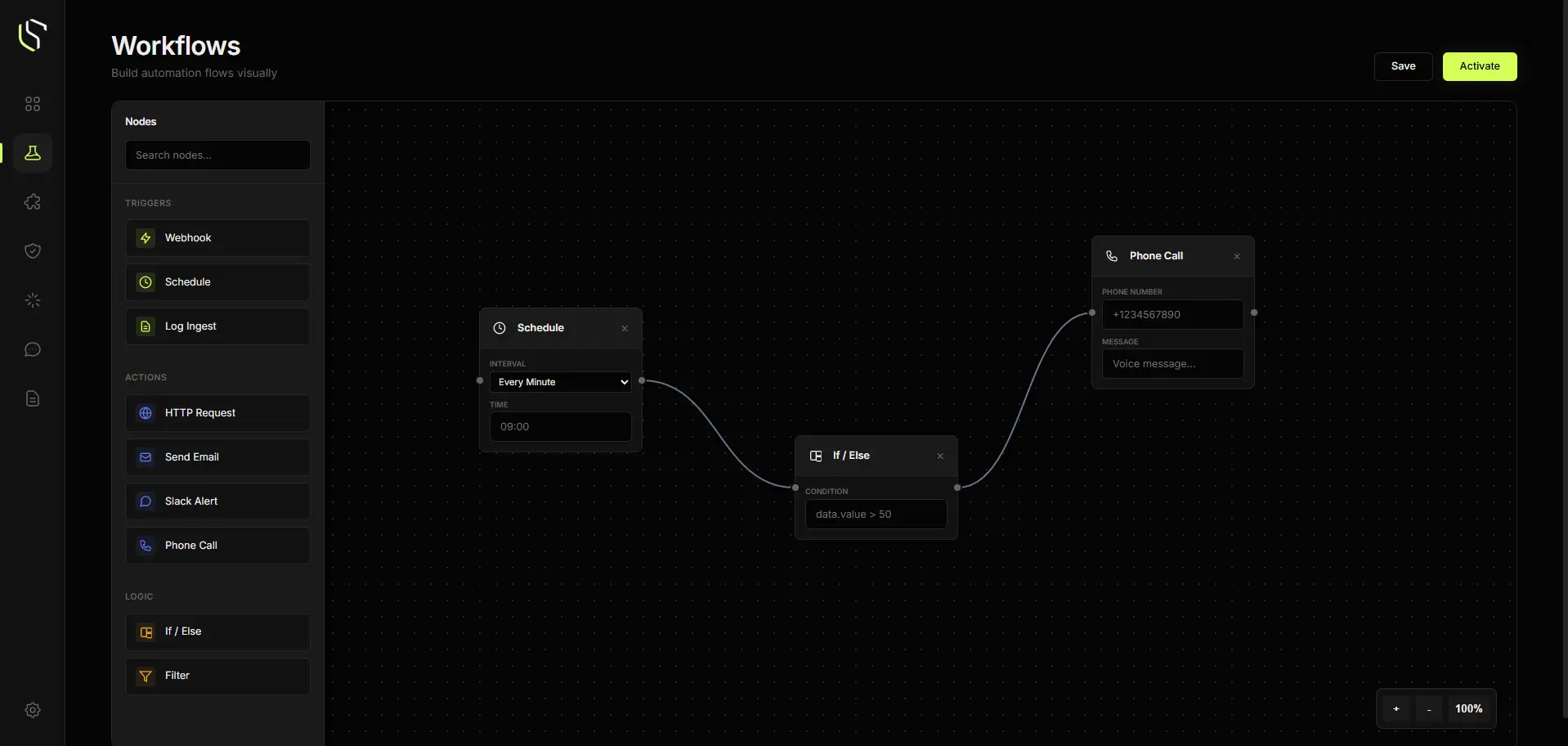
Workflow Module
Automated security policy orchestration. Visual workflow builder for creating, testing, and deploying security rules at scale across your entire infrastructure.
Learn moreCommon questions
Everything you need to know about Secbase.
How does the AI threat detection work?
Our neural networks analyze traffic patterns in real-time, identifying anomalies that deviate. Choose between local or cloud-based AI models that continuously learn from new threats and adapt to your specific environment.
Is my data used to train the global model?
No. We train our models using synthetic and public datasets to ensure your data remains completely private on your local infrastructure.
What happens during a breach attempt?
Secbase immediately detects and alerts your team through real-time monitoring and AI-powered threat analysis, generates automated response recommendations that you can deploy with a single click. Our 24/7 security specialists are available to guide you through response procedures and remediation steps."
Can I integrate with existing infrastructure?
Yes. Secbase is designed to overlay seamlessly with all major cloud providers, SIEM tools, and on-premise architectures. We offer pre-built integrations for security tools.
Join the Waitlist – Get early access when we launch
Share your email and we will send your invitation as soon as access opens.
We're in early access. Limited slots for demos.




